More actions
| Fusee Launcher | |
|---|---|
 | |
| General | |
| Author | Qyriad |
| Type | Payload senders (Software) |
| Version | 2019 |
| License | GPL-2.0 |
| Last Updated | 2019/04/18 |
| Links | |
| Download | |
| Website | |
| Source | |
The Fusée Launcher is a proof-of-concept arbitrary code loader for a variety of Tegra processors, which takes advantage of CVE-2018-6242 ("Fusée Gelée") to gain arbitrary code execution and load small payloads over USB.
The vulnerability is documented in the report subfolder.
User guide
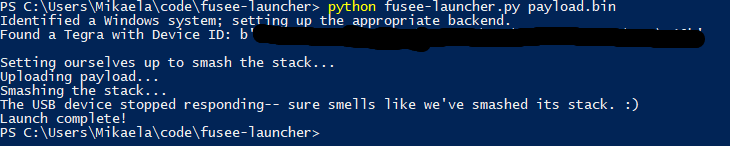
The main launcher is "fusee-launcher.py". Windows, Linux, macOS and FreeBSD are all natively supported. Instructions for Windows specifically can be found on the wiki.
With a Tegra device in RCM and connected via USB, invoke the launcher with the desired payload as an argument, e.g. ./fusee-launcher.py payload.bin. Linux systems currently require either that the Tegra device be connected to an XHCI controller (used with blue USB 3 ports) or that the user has patched their EHCI driver.
Screenshots
Credits
Fusée Gelée (CVE-2018-6242) was discovered and implemented by Kate Temkin (@ktemkin); its launcher is developed and maintained by Mikaela Szekely (@Qyriad) and Kate Temkin (@ktemkin).
Credit goes to:
- Qyriad - maintainership and expansion of the code.
- SciresM, motezazer - guidance and support.
- hedgeberg, andeor - dumping the Jetson bootROM.
- TuxSH - help with a first pass of bootROM RE.
- the ReSwitched team.
Love / greetings to:
- Levi / lasersquid.
- Aurora Wright.
- f916253.
- MassExplosion213.
- CVE-2018-6242 was also independently discovered by fail0verflow member shuffle2 as the "shofEL2" vulnerability-- so that's awesome, too.
External links
- GitHub - https://github.com/Qyriad/fusee-launcher
- GitHub - https://github.com/Qyriad/fusee-launcher/blob/master/report/fusee_gelee.md
- FAQ: Fusée Gelée - https://www.ktemkin.com/faq-fusee-gelee/
