More actions
| xyzzy | |
|---|---|
 | |
| General | |
| Author | bushing, DarkMatterCore |
| Type | System Tools |
| Version | 1.3.2 |
| License | GPL-2.0 |
| Last Updated | 2022/07/19 |
| Links | |
| Download | |
| Website | |
| Source | |
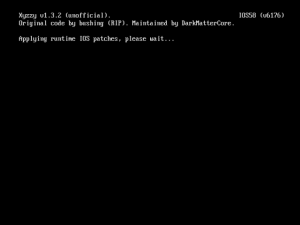
Xyzzy is a homebrew application that allows the extraction of the OTP and SEEPROM Encryption Keys.
This homebrew application which was meant as a replacement for the Tweezer Attack. It originally used PatchMii to download, patch, and use a version of IOS to extract the OTP Encryption keys for the Wii.
This modified version uses full hardware access through the HW_AHBPROT flag to read the OTP and SEEPROM chips, the System Menu binary and the ES module from the current IOS, in order to retrieve the console keys. Thus, it no longer installs a modified IOS11 nor uses PatchMii.
Other changes include:
- Compatibility with USB mass storage devices.
- Support for GCN controllers and newer WiiMotes.
- Retrieves SD IV, MD5 Blanker and MAC address.
- Besides generating a "keys.txt" file with a hexdump of every dumped key, which follows the format required by wad2bin, these files are also created:
- "device.cert" (raw device certificate dump).
- "otp.bin" (raw OTP memory dump).
- "seeprom.bin" (raw SEEPROM memory dump) (Wii only).
- "bootmii_keys.bin" (follows the BootMii keys.bin format) (Wii only).
- "vwii_sram_otp.bin" (raw vWii OTP bank 6 dump with Wii U OTP data) (Wii U only).
- "boot0.bin" (raw ARM boot0 Mask ROM dump).
Output files are saved to "/xyzzy/{console_id}" on the selected storage device.
Changelog
V1.3.2
- Removed trailing whitespaces in the codebase.
- Added boot0 Mask ROM dumping (as requested by @MasterLuma).
V1.3.1
- Fixed OTP reading under RVT-R units. Big thanks to @MasterLuma for reporting the *issue and testing the fix.
V1.3.0
- Added support for vWii System Menu Ancast image.
External links
- GitHub - https://github.com/DarkMatterCore/xyzzy-mod
- WiiBrew - https://wiibrew.org/wiki/Xyzzy
